Traditional GRC vs Vanta & Drata vs Derive: How GRC Tools Evolved
Traditional GRC vs Vanta vs Drata vs Derive: How GRC Tools Evolved
Traditional GRC tools organized the program. Vanta and Drata automated the proof. Derive turns cyber risk management into a living operating system.
GRC started as an integration idea. GRC as a concept can be traced back to the early 2000s, and NIST has long treated continuous monitoring as a core part of risk management. Those ideas mattered. But they did not automatically give cybersecurity teams a system that could tell them what to prioritize next, how much risk it would reduce, or how to prove impact in dollars.
That gap is exactly why the market evolved in stages. Traditional GRC tools like Archer and ServiceNow centralized controls, policies, assessments, and reporting. Next-gen GRC and compliance automation platforms like Vanta and Drata automated evidence collection and continuous control monitoring. Derive represents the next step: a cybersecurity risk and operations platform built to quantify risk, prioritize action, benchmark against peers, and update in real time as work gets done.
What traditional GRC tools like Archer and ServiceNow were built to do
Traditional GRC solved a real problem. Enterprises needed one place to manage policies, controls, assessments, audits, exceptions, and reporting across large organizations. Archer still positions itself as a configurable integrated risk management platform spanning audit, enterprise and operational risk, IT and security risk, regulatory compliance, and third-party governance. ServiceNow positions GRC similarly, with integrated risk, business continuity, privacy, and third-party risk on a shared data model with workflow automation.
That model is useful. It creates structure. It creates accountability. It gives teams a system of record. But for many cyber teams, it also becomes the place where work is documented, reviewed, and reported after the fact. The output is usually visibility into controls, workflows, and compliance status, not a financially grounded answer to which action reduces cyber risk the most right now.
In other words, traditional GRC gives you a place to put everything. It does not necessarily give you a living cyber risk decision system.
What Vanta and Drata changed
Vanta and Drata improved the category in an important way. They attacked the manual evidence problem.
Vanta now describes itself as a trust management platform built around compliance, risk, proof, and AI. Its current product language emphasizes continuous control monitoring, automated evidence collection, risk management, vendor risk, and real-time risk visibility. Drata positions itself as AI-native trust management with continuous compliance, integrated risk management, automated evidence collection, and real-time monitoring across controls and vendor risk.
That is a real leap forward from screenshots, spreadsheets, and last-minute audit scrambles. If your biggest pain is staying audit-ready, scaling across frameworks, proving trust to customers, or reducing the manual lift of compliance operations, Vanta and Drata can be a major improvement over traditional GRC. Their value is real.
But their center of gravity is still different from Derive’s.
The core question Vanta and Drata answer is, “Are our controls working, are we compliant, and can we prove it?” That is useful. It is just not the same as answering, “What should we do next to reduce expected loss, by how much, and how do we prove the business impact of that decision?”
Why continuous compliance is not continuous cyber risk monitoring
This is the part I need to explain clearly.
Traditional GRC made governance more organized.
Next-gen GRC made compliance more automated.
Neither one automatically turns cyber risk into a real-time, financially prioritized operating model.
A control can be mapped. A policy can be current. Evidence can be collected automatically. A framework can be green. And a cyber team can still have no defensible answer to the questions leadership actually asks:
What matters most right now?
Which control or workflow reduces loss the most?
How do we justify budget?
How do we benchmark against peers?
How do we show measurable cybersecurity investment ROI?
That is the difference between continuous compliance and continuous cyber risk monitoring. One continuously proves status. The other continuously informs decisions.
Why Derive is in a different category
Derive is not another GRC tool. Derive unites Risk, Governance, and Operations in one living system, so cyber teams can quantify risk, prioritize actions, benchmark against peers, and prove impact in real time. Derive’s platform is built around three connected modules - Risk, Governance, and Operations - with quantified cyber risk, control ownership and evidence, and built-in workflows operating together as a single system. We’re uncompromising in our approach to replace traditional GRC platforms with a measurable system that connects cyber risk to business outcomes.
The Risk module is about quantified cyber risk, forecasting, and prioritization in dollars. The Governance module centralizes controls, ownership, assets, accountability, maturity, and evidence. The Operations module runs built-in workflows like user access reviews, vendor risk, AI risk, and incident response, then feeds that operational activity back into the model so risk changes as work is completed, missed, or degraded. That is the critical difference.
Derive is not just tracking whether a control exists. It is designed to show whether the control is reducing expected loss, whether a workflow is moving the organization in the right direction, and which task should be prioritized for the greatest reduction in risk per dollar. Our mission is to quantify cyber risk in real dollars, benchmark against peers, run workflows that cut risk fast, and continuously update as threats, controls, and assets change.
Derive’s Peer Risk Benchmarks are also a major category divider. They’re built from more than 100,000 verified cyber incidents, loss data, and continuously updated threat intelligence, which then ground risk modeling, peer comparison, cybersecurity investment ROI, and board-ready cybersecurity reporting in real-world loss context rather than vague scoring.
This is also where CRQ becomes more useful. Cyber risk quantification matters. But quantification alone was never the finish line. The real value is using quantified cyber risk every day to drive cyber risk prioritization, governance decisions, operational workflows, and measurable loss reduction. Derive turns CRQ into action.
Want more insights?
Check out the Cyber Risk Management 2025: The Path to Effective Risk Prioritisation report
Where Archer, ServiceNow, Vanta, and Drata stop - and where Derive starts
Archer and ServiceNow are strongest when you need a broad enterprise governance and integrated risk management foundation.
Vanta and Drata are strongest when you need compliance automation, continuous evidence collection, trust workflows, and faster audit readiness.
Derive is strongest when your team needs a cyber risk platform that tells you exactly what to do next, benchmarks you against peers, updates in real time, and proves impact in dollars.
That is why Derive should not be positioned as “another GRC tool.” It is the category after next-gen GRC: cybersecurity risk and operations.
Why this matters for buyers right now
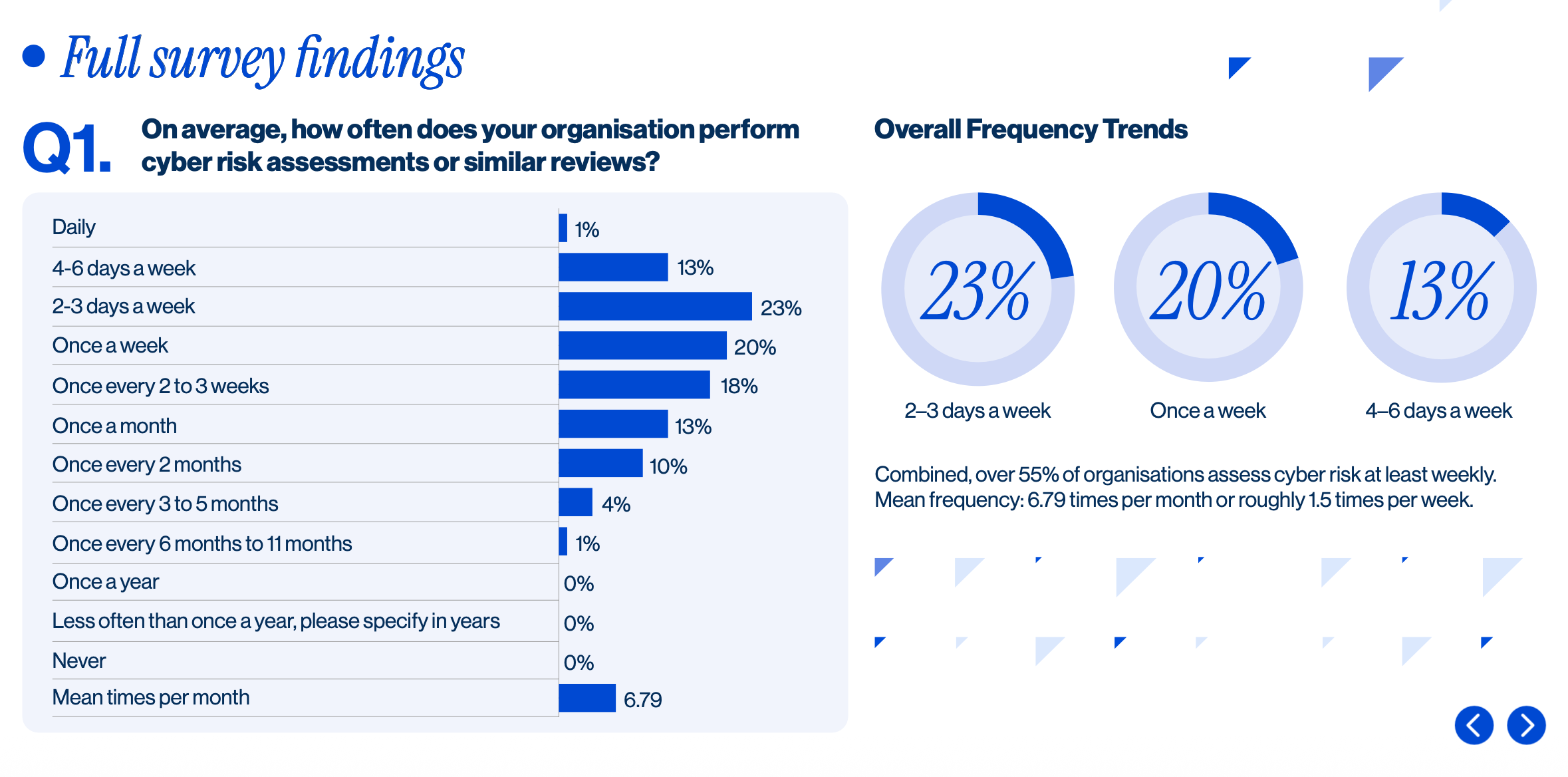
Our Cyber Risk Management 2025: The Path to Effective Risk Prioritisation report is useful proof for the narrative. It found 56% of organizations perform cyber risk assessments weekly or more often, 32% cite fragmented platforms as their biggest barrier to visibility and efficiency, and only 21% say results lead to clear prioritization of next steps. In other words, teams are active, but activity is not the same thing as clarity.
That is the buying problem I’m writing about today.
Security operations leads and GRC owners do not need more dashboards. They need to know exactly what to prioritize. They need continuous cyber risk monitoring instead of point-in-time assessment. They need peer risk benchmarks that make outside-in comparison credible. They need cybersecurity investment ROI that stands up in front of leadership. They need board-ready cybersecurity reporting that translates cyber work into financial impact. Derive is built for those outcomes.
The bottom line
Traditional GRC made cyber programs more organized.
Vanta and Drata made compliance programs more automated.
Derive makes cyber risk management active.
So the right conclusion for buyers is not that Archer, ServiceNow, Vanta, or Drata are useless. It is that they solve earlier-stage problems. If your real job is cyber risk prioritization, continuous cyber risk monitoring, and proving measurable business impact, Derive is the more complete answer.
Traditional GRC organizes.
Next-gen GRC automates.
Derive tells your team what to do next - and proves why.
FAQs
-
Archer and ServiceNow may already help structure governance. Derive is built for a different job: helping cyber teams make better decisions day to day. Derive unites Risk, Governance, and Operations in one living system, so your team can see what to prioritize next, how much loss an action can reduce, and how risk changes as work gets done.
-
Vanta and Drata are useful when compliance automation is the center of gravity. Derive goes further. Derive continuously monitors cyber risk, benchmarks it against peers, and ties workflows directly to measurable loss reduction. Instead of stopping at status, Derive tells cyber teams what to do next and proves the impact in dollars.
-
No. Derive starts with quantified cyber risk, then extends it into Governance and Operations. That means controls, ownership, evidence, and workflows live in the same platform, and risk updates automatically as activities happen, evidence changes, or controls degrade. CRQ is the foundation. Action is the outcome.
-
Yes. Derive maps risks and controls to DORA, NIS 2, SOC 2, and ISO 27001 while keeping quantified cyber risk at the core. The goal is not just to stay aligned to frameworks. The goal is to connect compliance work to real-world risk reduction and better cybersecurity investment decisions.
-
Derive models cyber risk in financial terms, benchmarks it against real-world peers, and shows which controls and workflows reduce loss and by how much. That gives teams a defensible way to justify spend, sequence work, and report results in the language of the business.